Question: 1
In the following options, which of the two attacks use similar attack methods, they will generate a large number of useless response packets, occupying network bandwidth,
Consume equipment resources?
Question: 2
Which of the following options is correct for the sequence of the flow-by-stream detection of AntiDDoS?
1. The Netflow analysis device samples the current network flow;
2. Send a drainage command to the cleaning center;
3. Discover the DDoS attack stream;
4.Netior: analysis equipment sends alarms to ATIC management center
5. The abnormal flow is diverted to the cleaning center for further inspection and cleaning;
6. The cleaning center sends the host route of the attacked target IF address server to the router to achieve drainage
7. The cleaning log is sent to the management center to generate a report;
8. The cleaned traffic is sent to the original destination server.
Question: 3
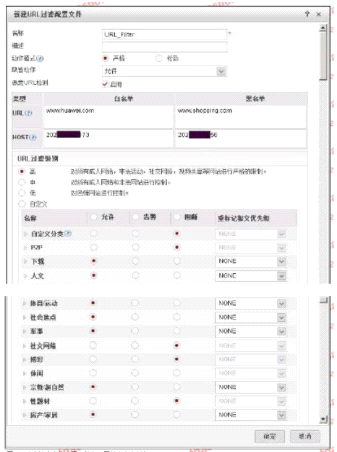
The following figure shows the configuration of the URL filtering configuration file. Regarding the configuration, which of the following statements is correct?
Question: 4
Which of the following types of attacks are DDoS attacks? 2I
Question: 5
The following figure is a schematic diagram of the detection file of the firewall and the sandbox system linkage.
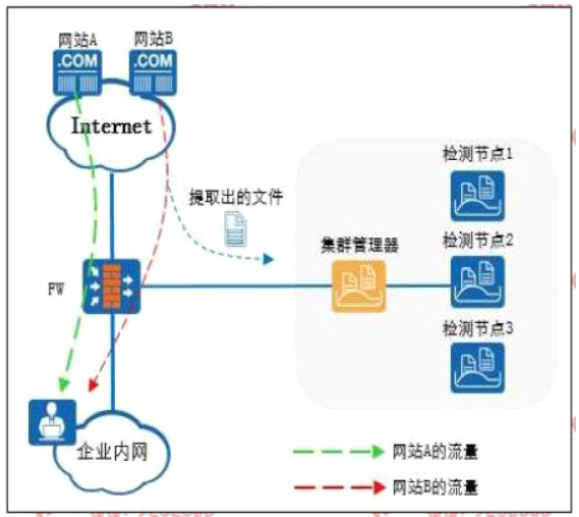
The Web reputation function is enabled on the firewall, and website A is set as a trusted website and website B is set as a suspicious website.
Which of the following statements is correct